Layered defense for dependencies: Why dependabot needs an upstream gatekeeper
TL;DR: Dependabot is great at keeping dependencies current, but update automation and ingestion control solve different problems. Cloudsmith acts as an upstream gatekeeper; ensuring packages are verified before they ever enter your environment. Together, they cover more of the supply chain than either does alone.
Let’s frame a scenario: a new dependency version is released. Within hours, Dependabot opens a pull request to upgrade your application.
The change looks routine. The PR is merged.
But this version wasn’t just an update - it was part of a coordinated malware campaign.
Before long, the compromised package has made its way into your build environment, cache layers, and developer workstations. Your security team is pulled into incident response, and a difficult question follows:
How did this get through so quickly, and how do we prevent it next time?
How dependency updates become a supply chain risk
To understand how this scenario unfolds, it’s worth breaking down what actually occurs between a dependency being published and a pull request being merged. When a new version of a package is released by a maintainer (or malicious actor in this case), it becomes immediately available in upstream registries such as npmjs, pypi, Maven Central, or DockerHub.
Tools like Dependabot continuously scan your repository’s dependency files for updates. As soon as a new version is detected, Dependabot compares it against what your application is currently using. If a valid upgrade path exists, it automatically opens a pull request with the updated version. From a developer’s perspective, everything looks normal:
- The dependency comes from a trusted source
- The version increment appears routine (ie. “It’s probably a patch or security fix”)
- The pull request follows a familiar, repeatable workflow
Nothing appears out of the ordinary - which is exactly how these attacks are designed.
At no point in this process is there a built-in mechanism to evaluate whether a newly released version is too new, potentially unverified, or part of a broader security incident without additional manual investigation. To make matters worse, it often takes time for security researchers to identify and report malicious packages, leaving a window where compromised versions can spread undetected.
That's not a criticism of the tool, it's a reminder that no single layer of automation was built to catch everything.
The problem isn’t automation; it’s the absence of an upstream control layer that determines when a dependency can be trusted and safely consumed
Dependabot cooldowns: Helpful, but not a complete safeguard
To address the risk of organizations rapidly adopting new dependencies, Dependabot offers a cooldown feature that allows platform teams to introduce a delay before opening pull requests for newly released dependency versions.
In practice, this means that even if a new version becomes available in the registry, Dependabot will intentionally wait for a defined period of time before suggesting the update through the pull request.
This provides an additional layer of protection:
- It gives the ecosystem the time to detect and flag malicious packages
- It reduces the likelihood of of immediately adopting unverified releases
- It helps avoid 0-Day exposure to newly published vulnerabilities
For many teams, this delay can significantly reduce risk. However, it’s important to recognize what this control does and does not protect against. Dependabot’s cooldown feature operates at the pull request level, meaning that it controls when an update is suggested, but it does not control what is ultimately available to your build systems or developers once a version is accessible in a registry.
Once a dependency version is published and reachable, it can still be:
- Pulled directly by developers
- Referenced in CI/CD pipelines
- Cached by build systems
- Downloaded outside of Dependabot entirely
In other words, Dependabot’s cooldown feature only influences one path to consumption, but not all paths. This naturally creates a gap: even with cooldown in place, a malicious package can still be consumed before it is ever flagged or blocked. While Dependabot’s cooldown can help reduce noise and delay exposure, they do not enforce a boundary around what dependencies your organization is allowed to consume.
If Dependabot’s cooldown helps reduce the speed of adoption, the next question becomes:
What controls when a dependency is allowed to exist in your environment at all?
Dependabot's cooldown helps slow the rate of adoption, but it doesn't control what dependencies are reachable in the first place. To close that gap, organizations need a control layer that sits upstream of their build systems entirely - one that determines whether a dependency is even available before any tool can request it.
Introducing an upstream gatekeeper for dependency security
This is where Cloudsmith comes in as your upstream gatekeeper. Instead of allowing direct, unrestricted access to upstream packages, Cloudsmith acts as a controlled gateway. With Cloudsmith Advanced Security, organizations can also introduce cooldown periods as policies to introduce time-based buffers to quarantine newly published dependency versions across a variety of different package formats.
For example, I currently work with a customer who has implemented a 5-day cooldown period for all npm packages with an updated version within that 5 day window. During this time, the customer can:
- Evaluate the package metadata
- Check security advisories for any potential malware
- Validate the upstream maintainer and perform additional reconnaissance
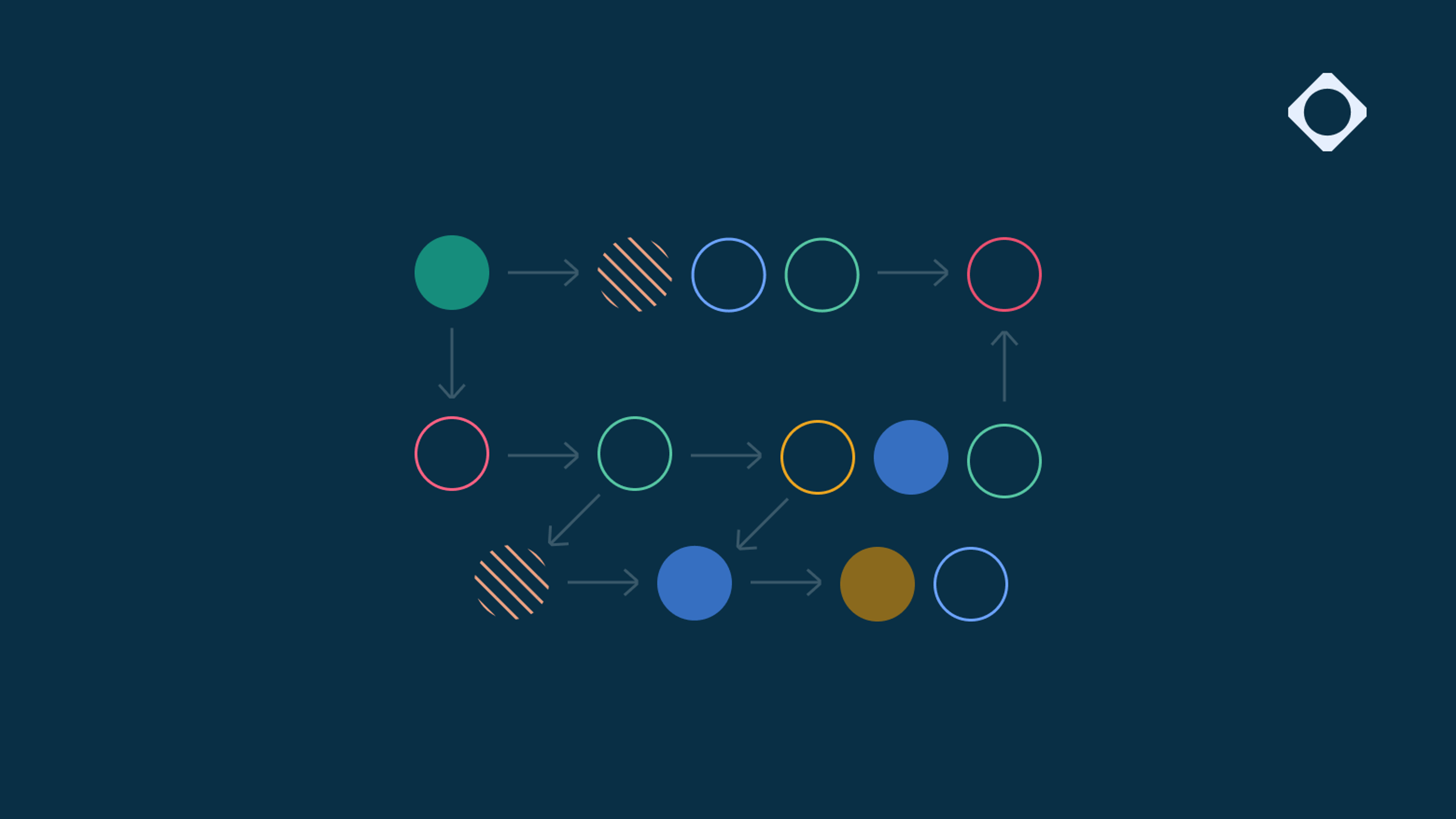
Only after the 5 day cooldown period is the package unquarantined and made available for download. When combined with Dependabot’s cooldown feature, organizations can layer the Dependabot cooldown with Cloudsmith’s to maximize security. Here’s an example workflow:
Let’s say an organization configures:
- A 5-day cooldown policy in Cloudsmith
- A 1-day cooldown policy in Dependabot
On Day 0, a new dependency version is released.
- Days 0-5: The version exists upstream, but Cloudsmith intentionally keeps it out of reach in quarantine state. It cannot be pulled by developers or CI/CD pipelines.
- Day 5: The version becomes available through Cloudsmith after the cooldown period has passed.
- Day 6: Dependabot is pointed to Cloudsmith, and now detects the newly available version and opens a pull request.
Cloudsmith controls when the version becomes consumable, while Dependabot controls when the version is proposed. Together, they ensure that updates are both safe and timely, without exposing the organization to newly released, potentially risky artifacts.
Bring It all together
Modern software delivery depends on automation, and tools like Dependabot have made keeping applications current easier than ever. But automation can only work safely within the boundaries set for it. Without an upstream control layer, every newly published dependency version is immediately exposed to your systems, trusted by default, not by design.
By pairing Dependabot with Cloudsmith's upstream cooldown policies, you create a model where trust is earned over time rather than assumed at the moment of release. Small in implementation, significant in impact: that shift is what allows teams to move fast without leaving the door open.
This layered approach is essential for organizations looking to strengthen their software supply chain security without slowing down development velocity.
More articles
Your upstream registry is not your friend: Why security teams are demanding package cooldown policies
TanStack npm packages compromised in Mini Shai-Hulud attack

Mini Shai-Hulud reaches Packagist: the intercom/intercom-php compromise explained

Closing the enforcement gap: Why visibility isn’t enough for supply chain security